2020. 10. 27. 17:45ㆍ카테고리 없음
macOS Server has long had a VPN service to allow client computers to connect to a network even when they’re out of the home or office. And as with many a service on macOS Server, this is one of the easiest VPN servers you’ll ever setup. The server was once capable of running the two most commonly used VPN protocols: PPTP and L2TP. And while PPTP is still accessible via the command line, L2TP is now configured by default when you setup the server using the Server app.
- If you are looking for low prices products, find in our store.
- If you searching for special discount you'll need to searching when special time come or holidays.
Our VPN service uses and requires the following ports for the communication: Windows Desktop, Mac Desktop and Android versions using OpenVPN with TCP and port 443 iOS, Mac AppStore and Microsoft Store versions using IPSEC with UDP port 4500 and ESP/UDP on Port 500 The communication to the backend API is done with TCP on port 443. I am using a Mac mini OS X Mountain Lion Server (10.8.5). My goal is to have the server's own VPN service running over L2TP only. The Mac mini is behind an AirPort Extreme (4th generation) AirPort Extreme has: static IPv4 address. No connection sharing (bridged mode) Back To My Mac disabled (as for all the Macs and AirPorts on the network). Nevertheless, I hope that this reviews about it Vpn Port Nubmer And Cisco Anyconnect Vpn Client For Mac Os X 10 8 will possibly be useful.
How do you download mods on minecraft for mac. Download compatible mods. Make sure you have your newly downloaded add-ons ready to be accessed. We will need to move these to a new folder for complete installation. Install mods by copying the files into the /mods/ folder. Select your mods and run them. Once you run your mods, you will see them applied directly to your game!
Setting Up The VPN Service In macOS ServerTo setup the VPN service, open the Server app and click on VPN in the Server app sidebar. The VPN Settings screen has a number of options available, as seen here.
The VPN Host Name field is used by administrators leveraging profiles. The setting used becomes the address for the VPN service in the Everyone profile. L2TP requires a shared secret or an SSL certificate. In this example, we’ll configure a shared secret by providing a password in the Shared Secret field. Additionally, there are three fields, each with an Edit button that allows for configuration:
- Client Addresses: The dynamic pool of addresses provided when clients connect to the VPN.
- DNS Settings: The name servers used once a VPN client has connected to the server. As well as the Search Domains configuration.
- Routes: Select which interface (VPN or default interface of the client system) that a client connects to each IP address and subnet mask over.
- Save Configuration Profile: Use this button to export configuration profiles to a file, which can then be distributed to client systems (macOS using the profiles command, iOS using Apple Configurator or both using Profile Manager).
- Shared Secret: A passphrase that must be supplied by the client prior to getting a username and password prompt.
Using The Command Line
I know, I’ve described ways to manage these services from the command line before. The serveradmin command can be used to manage the service as well as the Server app. The serveradmin command can start the service, using the default settings, with no further configuration being required:
sudo serveradmin start vpnAnd to stop the service:
sudo serveradmin stop vpn And to list the available options: sudo serveradmin settings vpnThe output of which shows all of the VPN settings available via serveradmin (which is many more than what you see in the Server app:
vpn:vpnHost = 'odr.krypted.com' vpn:Servers:com.apple.ppp.pptp:Server:Logfile = '/var/log/ppp/vpnd.log' vpn:Servers:com.apple.ppp.pptp:Server:VerboseLogging = 1 vpn:Servers:com.apple.ppp.pptp:Server:MaximumSessions = 128 vpn:Servers:com.apple.ppp.pptp:DNS:OfferedSearchDomains:_array_index:0 = 'jamfsw.corp' vpn:Servers:com.apple.ppp.pptp:DNS:OfferedServerAddresses:_array_index:0 = '10.10.16.200' vpn:Servers:com.apple.ppp.pptp:DNS:OfferedServerAddresses:_array_index:1 = '10.1.16.20' vpn:Servers:com.apple.ppp.pptp:DNS:OfferedServerAddresses:_array_index:2 = '8.8.8.8' vpn:Servers:com.apple.ppp.pptp:Radius:Servers:_array_index:0:SharedSecret = '1' vpn:Servers:com.apple.ppp.pptp:Radius:Servers:_array_index:0:Address = '1.1.1.1' vpn:Servers:com.apple.ppp.pptp:Radius:Servers:_array_index:1:SharedSecret = '2' vpn:Servers:com.apple.ppp.pptp:Radius:Servers:_array_index:1:Address = '2.2.2.2' vpn:Servers:com.apple.ppp.pptp:EAP:KerberosServicePrincipalName = 'vpn/odr.krypted.com@OSXSERVER.KRYPTED.COM' vpn:Servers:com.apple.ppp.pptp:enabled = no vpn:Servers:com.apple.ppp.pptp:Interface:SubType = 'PPTP' vpn:Servers:com.apple.ppp.pptp:Interface:Type = 'PPP' vpn:Servers:com.apple.ppp.pptp:PPP:LCPEchoFailure = 5 vpn:Servers:com.apple.ppp.pptp:PPP:DisconnectOnIdle = 1 vpn:Servers:com.apple.ppp.pptp:PPP:AuthenticatorEAPPlugins:_array_index:0 = 'EAP-RSA' vpn:Servers:com.apple.ppp.pptp:PPP:AuthenticatorACLPlugins:_array_index:0 = 'DSACL' vpn:Servers:com.apple.ppp.pptp:PPP:CCPEnabled = 1 vpn:Servers:com.apple.ppp.pptp:PPP:IPCPCompressionVJ = 0 vpn:Servers:com.apple.ppp.pptp:PPP:ACSPEnabled = 1 vpn:Servers:com.apple.ppp.pptp:PPP:LCPEchoEnabled = 1 vpn:Servers:com.apple.ppp.pptp:PPP:LCPEchoInterval = 60 vpn:Servers:com.apple.ppp.pptp:PPP:MPPEKeySize128 = 1 vpn:Servers:com.apple.ppp.pptp:PPP:AuthenticatorProtocol:_array_index:0 = 'MSCHAP2' vpn:Servers:com.apple.ppp.pptp:PPP:MPPEKeySize40 = 0 vpn:Servers:com.apple.ppp.pptp:PPP:AuthenticatorPlugins:_array_index:0 = 'DSAuth' vpn:Servers:com.apple.ppp.pptp:PPP:Logfile = '/var/log/ppp/vpnd.log' vpn:Servers:com.apple.ppp.pptp:PPP:VerboseLogging = 1 vpn:Servers:com.apple.ppp.pptp:PPP:DisconnectOnIdleTimer = 7200 vpn:Servers:com.apple.ppp.pptp:PPP:CCPProtocols:_array_index:0 = 'MPPE' vpn:Servers:com.apple.ppp.pptp:IPv4:OfferedRouteMasks = _empty_array vpn:Servers:com.apple.ppp.pptp:IPv4:DestAddressRanges:_array_index:0 = '10.10.23.255' vpn:Servers:com.apple.ppp.pptp:IPv4:DestAddressRanges:_array_index:1 = '10.10.23.254' vpn:Servers:com.apple.ppp.pptp:IPv4:OfferedRouteAddresses = _empty_array vpn:Servers:com.apple.ppp.pptp:IPv4:OfferedRouteTypes = _empty_array vpn:Servers:com.apple.ppp.pptp:IPv4:ConfigMethod = 'Manual' vpn:Servers:com.apple.ppp.l2tp:Server:LoadBalancingAddress = '1.2.3.4' vpn:Servers:com.apple.ppp.l2tp:Server:MaximumSessions = 128 vpn:Servers:com.apple.ppp.l2tp:Server:LoadBalancingEnabled = 0 vpn:Servers:com.apple.ppp.l2tp:Server:Logfile = '/var/log/ppp/vpnd.log' vpn:Servers:com.apple.ppp.l2tp:Server:VerboseLogging = 1 vpn:Servers:com.apple.ppp.l2tp:DNS:OfferedSearchDomains:_array_index:0 = 'jamfsw.corp' vpn:Servers:com.apple.ppp.l2tp:DNS:OfferedServerAddresses:_array_index:0 = '10.10.16.200' vpn:Servers:com.apple.ppp.l2tp:DNS:OfferedServerAddresses:_array_index:1 = '10.1.16.20' vpn:Servers:com.apple.ppp.l2tp:DNS:OfferedServerAddresses:_array_index:2 = '8.8.8.8' vpn:Servers:com.apple.ppp.l2tp:Radius:Servers:_array_index:0:SharedSecret = '1' vpn:Servers:com.apple.ppp.l2tp:Radius:Servers:_array_index:0:Address = '1.1.1.1' vpn:Servers:com.apple.ppp.l2tp:Radius:Servers:_array_index:1:SharedSecret = '2' vpn:Servers:com.apple.ppp.l2tp:Radius:Servers:_array_index:1:Address = '2.2.2.2' vpn:Servers:com.apple.ppp.l2tp:EAP:KerberosServicePrincipalName = 'vpn/odr.krypted.com@OSXSERVER.KRYPTED.COM' vpn:Servers:com.apple.ppp.l2tp:enabled = yes vpn:Servers:com.apple.ppp.l2tp:Interface:SubType = 'L2TP' vpn:Servers:com.apple.ppp.l2tp:Interface:Type = 'PPP' vpn:Servers:com.apple.ppp.l2tp:PPP:LCPEchoFailure = 5 vpn:Servers:com.apple.ppp.l2tp:PPP:DisconnectOnIdle = 1 vpn:Servers:com.apple.ppp.l2tp:PPP:AuthenticatorEAPPlugins:_array_index:0 = 'EAP-KRB' vpn:Servers:com.apple.ppp.l2tp:PPP:AuthenticatorACLPlugins:_array_index:0 = 'DSACL' vpn:Servers:com.apple.ppp.l2tp:PPP:VerboseLogging = 1 vpn:Servers:com.apple.ppp.l2tp:PPP:IPCPCompressionVJ = 0 vpn:Servers:com.apple.ppp.l2tp:PPP:ACSPEnabled = 1 vpn:Servers:com.apple.ppp.l2tp:PPP:LCPEchoInterval = 60 vpn:Servers:com.apple.ppp.l2tp:PPP:LCPEchoEnabled = 1 vpn:Servers:com.apple.ppp.l2tp:PPP:AuthenticatorProtocol:_array_index:0 = 'MSCHAP2' vpn:Servers:com.apple.ppp.l2tp:PPP:AuthenticatorPlugins:_array_index:0 = 'DSAuth' vpn:Servers:com.apple.ppp.l2tp:PPP:Logfile = '/var/log/ppp/vpnd.log' vpn:Servers:com.apple.ppp.l2tp:PPP:DisconnectOnIdleTimer = 7200 vpn:Servers:com.apple.ppp.l2tp:IPSec:SharedSecretEncryption = 'Keychain' vpn:Servers:com.apple.ppp.l2tp:IPSec:LocalIdentifier = ' vpn:Servers:com.apple.ppp.l2tp:IPSec:SharedSecret = 'com.apple.ppp.l2tp' vpn:Servers:com.apple.ppp.l2tp:IPSec:AuthenticationMethod = 'SharedSecret' vpn:Servers:com.apple.ppp.l2tp:IPSec:RemoteIdentifier = ' vpn:Servers:com.apple.ppp.l2tp:IPSec:IdentifierVerification = 'None' vpn:Servers:com.apple.ppp.l2tp:IPSec:LocalCertificate = <> vpn:Servers:com.apple.ppp.l2tp:IPv4:OfferedRouteMasks = _empty_array vpn:Servers:com.apple.ppp.l2tp:IPv4:DestAddressRanges:_array_index:0 = '10.10.23.128' vpn:Servers:com.apple.ppp.l2tp:IPv4:DestAddressRanges:_array_index:1 = '10.10.23.254' vpn:Servers:com.apple.ppp.l2tp:IPv4:OfferedRouteAddresses = _empty_array vpn:Servers:com.apple.ppp.l2tp:IPv4:OfferedRouteTypes = _empty_array vpn:Servers:com.apple.ppp.l2tp:IPv4:ConfigMethod = 'Manual' vpn:Servers:com.apple.ppp.l2tp:L2TP:Transport = 'IPSec' vpn:Servers:com.apple.ppp.l2tp:L2TP:IPSecSharedSecretValue = 'Yq!XdGsVyAY?o;9jnj To disable L2TP, set vpn:Servers:com.apple.ppp.l2tp:enabled to no:
sudo serveradmin settings vpn:Servers:com.apple.ppp.l2tp:enabled = nosudo serveradmin settings vpn:Servers:com.apple.ppp.l2tp:PPP:DisconnectOnIdle = 10By default, each protocol has a maximum of 128 sessions, configureable using vpn:Servers:com.apple.ppp.pptp:Server:MaximumSessions:
Free Vpn For Macs
sudo serveradmin settings vpn:Servers:com.apple.ppp.pptp:Server:MaximumSessions = 200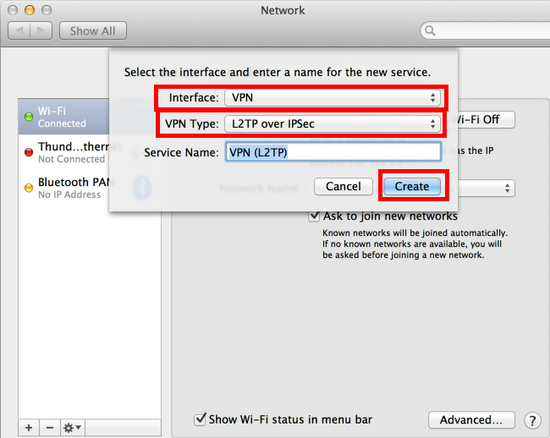 To see the state of the service, the pid, the time the service was configured, the path to the log files, the number of clients and other information, use the fullstatus option:
To see the state of the service, the pid, the time the service was configured, the path to the log files, the number of clients and other information, use the fullstatus option: Vpn For Mac Os
sudo serveradmin fullstatus vpnWhich returns output similar to the following:
vpn:servicePortsAreRestricted = 'NO' vpn:readWriteSettingsVersion = 1 vpn:servers:com.apple.ppp.pptp:AuthenticationProtocol = 'MSCHAP2' vpn:servers:com.apple.ppp.pptp:CurrentConnections = 0 vpn:servers:com.apple.ppp.pptp:enabled = yes vpn:servers:com.apple.ppp.pptp:MPPEKeySize = 'MPPEKeySize128' vpn:servers:com.apple.ppp.pptp:Type = 'PPP' vpn:servers:com.apple.ppp.pptp:SubType = 'PPTP' vpn:servers:com.apple.ppp.pptp:AuthenticatorPlugins = 'DSAuth' vpn:servers:com.apple.ppp.l2tp:AuthenticationProtocol = 'MSCHAP2' vpn:servers:com.apple.ppp.l2tp:Type = 'PPP' vpn:servers:com.apple.ppp.l2tp:enabled = yes vpn:servers:com.apple.ppp.l2tp:CurrentConnections = 0 vpn:servers:com.apple.ppp.l2tp:SubType = 'L2TP' vpn:servers:com.apple.ppp.l2tp:AuthenticatorPlugins = 'DSAuth' vpn:servicePortsRestrictionInfo = _empty_array vpn:health = _empty_dictionary vpn:logPaths:vpnLog = '/var/log/ppp/vpnd.log' vpn:configured = yes vpn:state = 'STOPPED' vpn:setStateVersion = 1Security folk will be stoked to see that the shared secret is shown in the clear using:
vpn:Servers:com.apple.ppp.l2tp:L2TP:IPSecSharedSecretValueConfiguring Users For VPN Access
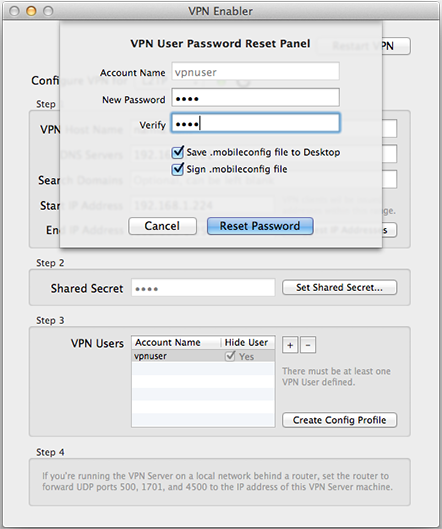
Each account that accesses the VPN server needs a valid account to do so. To configure existing users to use the service, click on Users in the Server app sidebar.
Ports For Vpn Mac Download
At the list of users, click on a user and then click on the cog wheel icon, selecting Edit Access to Services.
At the Service Access screen will be a list of services that could be hosted on the server; verify the checkbox for VPN is highlighted for the user. If not, click Manage Service Access, click Manage and then check the VPN box.
Setting Up Client Computers
As you can see, configuring the VPN service in macOS Server 5.4 (running on High Sierra) is a simple and straight-forward process – much easier than eating your cereal with a fork and doing your homework in the dark. Configuring clients is as simple as importing the profile generated by the service. However, you can also configure clients manually. To do so on a Mac, open the Network System Preference pane.
From here, click on the plus sign (“+”) to add a new network service.

Ports For Vpn Mac Client
At the prompt, select VPN in the Interface field and then either PPTP or L2TP over IPSec in the VPN Type. Then provide a name for the connection in the Service Name field and click on Create.At the list of network interfaces in the Network System Preference pane, provide the hostname or address of the server in the Server Address field and the username that will be connecting to the VPN service in the Account Name field. If using L2TP, click on Authentication Settings.
At the prompt, provide the password entered into the Shared Secret field earlier in this article in the Machine Authentication Shared Secret field and the user’s password in the User Authentication Password field. When you’re done, click OK and then provided you’re outside the network and routeable to the server, click on Connect to test the connection.
Ports For Vpn Tunnels
Conclusion
Use Vpn On Mac
Setting Up the VPN service in macOS Server 5.4 is as simple as clicking the ON button. But much more information about using a VPN can be required. The natd binary is still built into OS X at /usr/sbin/natd and can be managed in a number of ways. And if you’re using an Apple AirPort as a router (hopefully in a very small environment) then the whole process of setting this thing up should be super-simple.